Maze Writeup - Cyber Apocalypse 2024
→ 1 Introduction
This writeup covers the Maze Hardware challenge from the Hack The Box Cyber Apocalypse 2024 CTF, which was rated as having a ‘very easy’ difficulty. The challenge involved finding a flag within the file system of a printer.
The description of the challenge is shown below.
→ 2 Artifacts Summary
The downloaded artifact had the following hash:
$ shasum -a256 hardware_maze.zip
2741ed17e6a4968927f360d0be8240723fe0e374d2ee306e2ccd3c02b51a97a3 hardware_maze.zipThe zip file contained a number of directories but only a handful of files:
$ unzip hardware_maze.zip
Archive: hardware_maze.zip
creating: hardware_maze/
creating: hardware_maze/fs/
creating: hardware_maze/fs/webServer/
creating: hardware_maze/fs/webServer/lib/
extracting: hardware_maze/fs/webServer/lib/security
extracting: hardware_maze/fs/webServer/lib/keys
creating: hardware_maze/fs/webServer/home/
inflating: hardware_maze/fs/webServer/home/hostmanifest
inflating: hardware_maze/fs/webServer/home/device.html
creating: hardware_maze/fs/webServer/objects/
creating: hardware_maze/fs/webServer/permanent/
creating: hardware_maze/fs/webServer/default/
inflating: hardware_maze/fs/webServer/default/csconfig
creating: hardware_maze/fs/saveDevice/
creating: hardware_maze/fs/saveDevice/SavedJobs/
creating: hardware_maze/fs/saveDevice/SavedJobs/InProgress/
inflating: hardware_maze/fs/saveDevice/SavedJobs/InProgress/Factory.pdf
creating: hardware_maze/fs/saveDevice/SavedJobs/KeepJob/
creating: hardware_maze/fs/PJL/
creating: hardware_maze/fs/PostScript/→ 3 Obtaining the flag
The number of bytes in each file was summarized.
$ wc -c $(find hardware_maze -type f)
1299238 hardware_maze/fs/saveDevice/SavedJobs/InProgress/Factory.pdf
4520 hardware_maze/fs/webServer/default/csconfig
0 hardware_maze/fs/webServer/lib/keys
0 hardware_maze/fs/webServer/lib/security
230 hardware_maze/fs/webServer/home/hostmanifest
165 hardware_maze/fs/webServer/home/device.html
1304153 total
Examining each non-empty file in turn, the flag was found in
Factory.pdf:
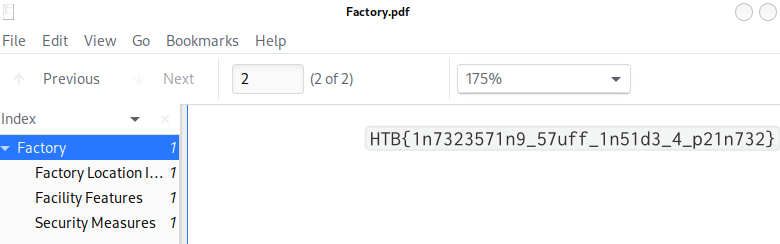
→ 4 What does the challenge have to do with hardware?
Based on the excerpt of
hardware_maze/fs/webServer/default/csconfig shown below,
and even the flag itself, the fs directory contains the
files from an HP LaserJet printer file system that runs an embedded web
server. The
hardware_maze/fs/saveDevice/SavedJobs/InProgress/Factory.pdf
file indicates the printer stores documents submitted for printing on
the file system. Thus, if an attacker manages to gain access to the file
system, perhaps due to a vulnerability in the web server, they can
potentially read sensitive files submitted for printing.
%
% ChaiServer configuration file
%
% This file contains the csconfig file for the laserjet ChaiServer
%
Port 80 timeout 0
%
% Document Root
% Our document root points to a link on RAM disk. This link will either point
% to the default webServer directory on the ROM disk or to a directory on
% some permanant storage device if it is installed
%
DocumentRoot "file:////hpmnt/webServer/home/"
% ExtraPath Information
ExtraPath hp/device
% Platform Type
PlatformType Vectra
% Number of typers to start
StartTypers 4
% Keep-Alive parameters
KeepAlive Timeout 1 MaxConnections 5
% Keystore implementation class
KEYSTORE_IMPL hp.laserjet.keystoremanager.DeviceKeyStoreImpl
% The following packages exist
Worker "hp/chaiserver/webserver/WebServer"
{
StartWorkers 2
MimeType hp/webserver webserver
MimeType text/html html
MimeType text/plain txt java
MimeType image/gif gif
MimeType image/jpeg jpg jpeg
MimeType application/zip zip
MimeType text/css css
MimeType application/x-javascript js
MimeType application/java-archive jar
Param "HOMEPAGE_OBJECT" "this.LCDispatcher"
}
<snip/>→ 5 Conclusion
The flag was submitted and the challenge was marked as pwned